TL; DR
Compliance archiving defines how regulated records are preserved once operational systems change or disappear. Enterprises fail the regulations when archives rely on legacy applications, lose metadata, or cannot produce records quickly during audits.
A durable compliance archive is independent, immutable, searchable, and built to withstand regulatory scrutiny.
In every organization, with time, applications are upgraded, replaced, or decommissioned. Vendors change. Data models evolve. Teams reorganize. Key employees leave.
What an institution believed, decided, approved, or executed five or ten years ago becomes difficult to reconstruct with confidence. Yet regulators continue to ask questions long after those changes occur. This is the gap compliance archiving is meant to close.
This is why compliance archiving is fundamentally different from backup, retention policies, or low-cost storage. Its purpose is not recovery but proof.
How is Compliance Archiving Different from Standard Data Archiving?
| Aspect | Standard Data Archiving | Compliance Archiving |
|---|---|---|
| Primary purpose | Operational efficiency and cost reduction | Regulatory accountability and evidence preservation |
| Main goal | Move inactive data out of production systems | Prove what happened, when, and how |
| Design focus | Storage optimization and system performance | Long-term access, integrity, and verifiability |
| Data integrity | Not designed for evidentiary assurance | Must remain complete and unaltered |
| Retrieval expectation | Occasional, internal use | On-demand regulatory access under scrutiny |
| Dependency on source systems | May rely on original data formats, schemas, or contextual knowledge from source systems | Independent of source systems over time |
| Regulatory suitability | Not sufficient on its own | Explicitly designed to meet regulatory expectations |
What Regulators Actually Expect to Access
This is where many organizations get uncomfortable because access, context, and verification are harder than expected once time has passed.
What do regulators mean by “regulatory access”?
Regulatory access means the ability to retrieve specific records on request, within a reasonable timeframe, and in a form that can be reviewed independently.
It is not enough for data to exist somewhere in the organization. Regulators expect access that is scoped, timely, and reliable. They must be able to ask for a defined set of records and receive them without requiring system reconstruction, manual intervention across teams, or dependence on legacy platforms.
If records exist but cannot be produced in context, regulators do not consider them accessible.
What types of data fall under compliance archiving requirements?
Compliance archiving applies to any data that supports, evidences, or explains regulated activity. This commonly includes transactional records, account data, communications, approvals, audit trails, and supervisory records that are required to comply with industry or sector-specific regulatory standards.
The determining factor is not the file format or system of origin. If a record may be needed to demonstrate compliance, explain a decision, or reconstruct activity during an examination, it falls within scope.
What evidence do regulators expect from a compliance archive?
Just as important as the type of records matters for the evidence, it also includes the surrounding metadata that establishes when records were created, how they were handled, and whether they remained intact over time.
A compliance archive is expected to support reconstruction. Regulators want to understand what happened, not just see fragments of data.
What happens if archived data cannot be produced during an audit?
When requested records cannot be produced, regulators typically treat this as a compliance failure, regardless of intent. From a regulatory perspective, data that cannot be accessed when needed may as well not exist. This is why regulatory access is the defining test of compliance archiving. Everything else is secondary.
How long must data be retained for regulatory compliance? Which regulations require enterprises to maintain long-term, accessible compliance archives?
Retention periods are defined by regulation and vary by industry, jurisdiction, and record type. Some records must be retained for a fixed number of years, while others must be preserved for the life of the customer relationship or longer.
The table below highlights major regulations that commonly drive long-term compliance archiving strategies across regions and industries.
| Regulation / Framework | Region / Jurisdiction | Primary Scope | Why Compliance Archiving Matters |
|---|---|---|---|
| DPDPA | India | Personal data protection | Organizations must demonstrate lawful handling, retention, and deletion decisions over time |
| GDPR | European Union | Personal data protection | Regulators expect proof of purpose limitation, retention control, and access governance |
| PDPL | Saudi Arabia | Personal data protection | Long-term accountability for how personal data is stored, accessed, and protected |
| PDPA (ASEAN) | Southeast Asia | Personal data protection | Enterprises must preserve records to justify historical data processing decisions |
| APPI | Japan | Personal data protection | Historical records must support regulatory inquiries and audit reviews |
| DIFC Data Protection Law | DIFC, UAE | Regulated financial entities | Secure, auditable access to regulated data is mandatory |
| SEC 17a-4 | United States | Broker-dealers | Financial records must remain immutable and accessible for regulatory review |
| FINRA Rules | United States | Financial services | Communications and transaction records are examined years after creation |
| SOX | United States | Public companies | Financial records must support long-term accountability and auditability |
| SAMA Regulations | Saudi Arabia | Banking and financial institutions | Regulators require provable historical compliance and record integrity |
| HIPAA | United States | Healthcare | Access logs, records, and controls must remain auditable over time |
Why General-Purpose Archiving Falls Short of Compliance Needs
Many organizations believe they have compliance archiving covered because data is being stored, retained, or backed up somewhere. That confidence usually holds until the first serious regulatory request arrives.
Why do compliance archives fail years after deployment?
Compliance archives often fail not because they were poorly implemented, but because they were designed around short-term assumptions.
Archives that depend on original applications, proprietary tooling, or manual processes degrade quietly until retrieval becomes risky, slow, or impossible. These failures surface only when regulators ask questions years later.
What are the most common compliance archiving failures during audits?
The same patterns appear repeatedly during examinations:
- Records exist but cannot be located quickly
- Data is incomplete or inconsistent across time
- Archived records lack sufficient metadata to establish context
- Access requires restoring legacy systems or custom workflows
- Integrity cannot be independently verified
What breaks when archived data is tied to decommissioned systems?
When archived data remains tied to the systems that created it, long-term access becomes fragile. Once those systems are decommissioned, retrieving records turns into a reconstruction exercise. This introduces delays, dependencies, and uncertainty precisely when regulators expect clarity.
A compliance archive that cannot stand on its own inherits the failure modes of every system it depends on. Over time, those dependencies become the archive’s weakest point. This is why general approaches create a false sense of security. They look sufficient while systems are active, and collapse when history is tested.
Compliance-Enabled Archiving Requirements
A compliance-enabled archive therefore, requires a minimum set of security, governance, and data protection capabilities that support regulatory access without exposing regulated data to unnecessary risk.
What are the core requirements for compliance-enabled archiving?
- Data security and privacy controls: Sensitive records must remain protected even while retained for long periods. This includes encryption of archived data and controlled exposure of fields through masking, ensuring that regulatory access does not become a data-leak risk.
- Access control and role enforcement: Compliance archives must enforce role-based access so that only authorized users can view or retrieve regulated records. Access rights must persist through organizational changes and be auditable over time.
- Governed storage and retention enforcement: Compliance archiving requires more than durable storage. Archives must support retention enforcement, secure storage tiers, and purge operations that remain aligned with regulatory requirements and base systems.
- Metadata and schema enforcement: Archived records must retain structural and contextual metadata, so they remain interpretable and searchable years later. Without enforced schemas and metadata layers, archives degrade into disconnected files that fail regulatory review.
- Data anonymization and tokenization where required: In environments where personal or sensitive data must be preserved but not exposed, archives should support anonymization and tokenization mechanisms. These controls allow organizations to retain evidence while reducing privacy risk during access or analysis.
Together, these capabilities ensure that archived data remains secure, governed, and reviewable, rather than simply stored.
Explore how Archon Data Store enables secure, governed compliance archiving built for regulatory scrutiny.
What a Compliant Archive Must Support Across Communication Channels?
Email archiving compliance: Email remains a primary source of regulatory evidence. A compliant archive must preserve message content, attachments, timestamps, sender and recipient data, and access history in a way that remains searchable and verifiable long after mail systems change.
Microsoft 365 and Office 365 compliance archiving: Native retention and eDiscovery features support short-term governance but remain tightly coupled to the platform. Long-term compliance requires independent preservation so historical email records remain accessible even as tenants, licenses, or service models evolve.
Microsoft Teams compliance archiving: Teams data spans chats, channels, files, and integrations. A compliant archive must preserve conversations with sufficient context to reconstruct interactions after teams or users are removed.
Slack and chat tool compliance archiving: High-volume messaging platforms introduce challenges around edits, deletions, threads, and reactions. Compliance archiving must capture conversations as regulated records, not just export messages.
Compliance video and meeting archiving: Recordings, transcripts, and related artifacts increasingly form part of regulatory evidence. Archives must preserve these assets alongside metadata that establishes timing, participants, and access history.
Multi-channel compliance archiving: A defensible compliance archive consolidates communication records across platforms into a unified evidentiary view. This allows regulators to review activity holistically rather than navigating fragmented, tool-specific datasets.
As communication ecosystems continue to expand, compliance archiving shifts from managing tools to preserving conversations, context, and accountability across channels.
Who Owns Compliance Archiving Within an Enterprise?
By this point, the technical and regulatory mechanics of compliance archiving are usually clear. What is less clear, and more consequential, is who inside the organization is actually responsible for making it work over time.
No single function owns compliance archiving outright, and that is precisely where risk begins.
Compliance archiving sits at the intersection of regulatory obligation, legal exposure, and technical execution. Compliance teams understand what must be preserved. Legal teams understand why it matters. IT teams control the systems that make it possible.
When ownership is not explicitly defined across these groups, compliance archiving becomes an orphaned responsibility. In those environments, failures are not hypothetical. They are inevitable.
How do compliance, IT, and legal teams share responsibility?
Effective compliance archiving operates on shared but clearly defined responsibilities.
- Compliance teams define record types, retention requirements, and regulatory expectations
- Legal teams interpret risk, oversee defensibility, and guide responses to investigations
- IT teams design, operate, and secure the systems that preserve and provide access to records.
Problems arise when these roles are assumed rather than documented. Without alignment, archives drift away from regulatory intent while still appearing operationally sound.
How do organizations test compliance archive readiness before audits?
Organizations that treat audits as the first test of their archive usually discover problems too late.
Readiness is tested by simulating regulatory requests. This includes:
- Identifying specific record sets
- Measuring retrieval time
- Verifying completeness
- Confirming the records can be reviewed without system reconstruction or manual intervention
What metrics indicate a mature compliance archiving program?
Mature compliance archiving indicators include
- Consistent retrieval times
- Completeness of historical records
- Verified integrity controls,
- Ability to respond to regulatory requests without escalating across teams or rebuilding environments
When should enterprises modernize their compliance archiving strategy?
Enterprises should revisit their compliance archiving strategy when systems are being retired, platforms are being consolidated, regulations evolve, or regulatory scrutiny increases—waiting until an audit exposes gaps forces reactive fixes under pressure.
Modernization is not an admission of failure. It is recognition that compliance archiving must evolve as the organization does.
The Architecture of a Real Compliance Archive
A real compliance archive is not defined by a single technology or deployment model. It is defined by architectural choices that assume change is inevitable and design around it. The goal is durability of access, not convenience of implementation.
At a minimum, a defensible compliance archive is built around five non-negotiable principles.
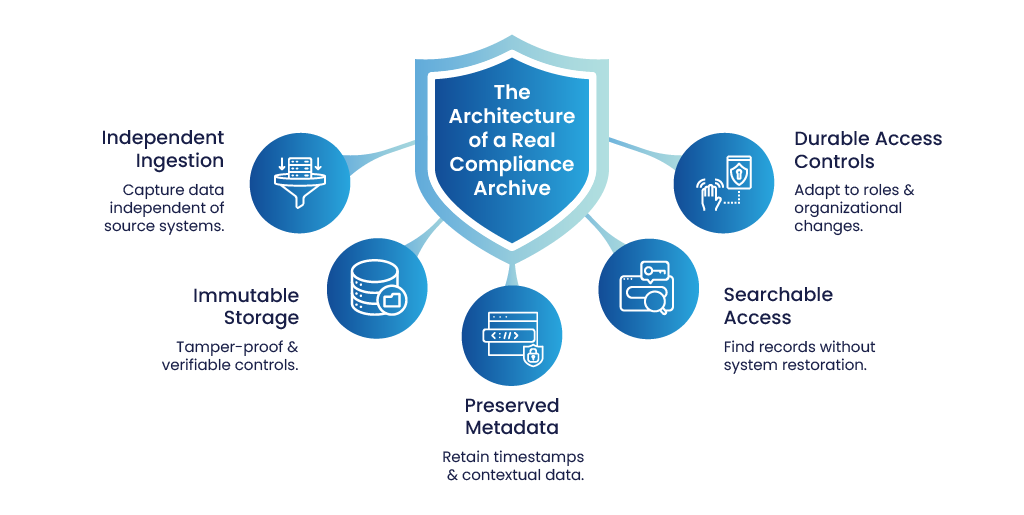
- First, ingestion must be independent of source systems: Data must be captured in a way that does not rely on the long-term availability of the application that created it. Source systems are transient by nature. Archives that inherit their dependencies inherit their failure modes. Independence ensures records remain accessible even after systems are upgraded, replaced, or retired.
- Second, storage must be immutable with verifiable controls: Once records enter the archive, they must be protected from alteration, deletion, or silent overwrite. Immutability is not just a configuration setting. It must be enforceable and demonstrable, with controls that can be explained and verified during an audit. This is what turns stored data into evidence.
- Third, metadata must be preserved alongside content: Content without context has limited regulatory value. A real compliance archive preserves timestamps, source identifiers, ownership details, relationships, and other metadata that allow records to be understood and reconstructed years later. Without this, archives degrade into disconnected files that raise more questions than they answer.
- Fourth, records must be searchable without restoring systems: Regulatory access cannot depend on legacy environments. Search and retrieval must work directly against the archive itself. This is what enables timely, scoped responses under audit pressure and prevents access from becoming an operational risk.
- Fifth, access controls must survive organizational change: People leave. Roles change. Teams reorganize. A compliance archive must support controlled access based on roles and authority, not individual tenure. Regulatory access should remain consistent even as the organization evolves.
When these principles are absent, archives tend to fail quietly over time. The questions below address where those failures usually originate.
How do enterprises ensure archived data remains searchable years later?
Archived data must be indexed and queried within the archive itself, using formats and services that are designed for longevity. When search depends on restoring old systems or replaying historical pipelines, it becomes brittle and slow.
Enterprises that plan for long-term searchability treat the archive as a primary access surface, not a cold storage tier.
What access controls are required for compliance archives?
Compliance archives require access controls that are auditable, role-based, and durable. Access should be granted based on authority, not individual familiarity with systems. Controls must support segregation of duties, logging of access activity, and continuity through organizational change. When access depends on informal processes or legacy permissions, regulatory confidence erodes quickly.
How Do Enterprises Operationalize This Architecture in Practice?
Designing a compliance archive around these principles is one thing. Operating it consistently over the years, across changing systems and regulations, is where most organizations struggle.
This is where platforms like Archon are typically introduced. Not as a storage layer, but as a compliance archive of record designed explicitly around regulatory access and longevity.
In practice, Archon is used to:
- Ingest records independently from source systems, so archives remain accessible even after applications are upgraded or retired
- Enforce immutability with verifiable controls that can be demonstrated during audits
- Preserve metadata alongside content, ensuring records retain context and evidentiary value over time
- Provide direct search and retrieval from the archive itself, without relying on legacy system restoration
- Maintain role-based, auditable access controls that remain stable despite organizational change
The emphasis is not on replacing existing systems, but on decoupling long-term regulatory evidence from operational volatility. This allows enterprises to retire, migrate, or modernize applications without putting historical compliance at risk.
In other words, platforms like Archon exist to make the architecture described above sustainable, not aspirational.
Want to assess whether your current archive would meet regulatory access expectations five or ten years from now?
Talk to a compliance data specialist to review your archiving architecture and identify long-term access risks before an audit does.