TL & DR;
HIPAA compliance rarely breaks down in live EHR systems; it breaks down when PHI becomes historical. As data moves into archives, backups, exports, and retired platforms, access controls weaken, audit trails fragment, and retention enforcement becomes difficult to prove.
HIPAA applies to inactive PHI in the same way it applies to active PHI, and regulators evaluate compliance based on evidence, not intent. Organizations must be able to demonstrate who accessed PHI, why it was retained, and how controls persisted after systems changed.
A compliance-grade governance layer that centralizes historical PHI, enforces metadata-driven access and retention, and preserves immutable audit trails enables healthcare organizations to reduce regulatory risk while modernizing and safely decommissioning legacy systems.
Healthcare organizations typically maintain strong security controls over live EHR systems. HIPAA compliance risk emerges later, when patient data moves into archives, backups, exports, and decommissioned applications that continue to store PHI long after clinical use ends.
HIPAA applies to historical PHI in the same way it applies to active PHI, which means compliance obligations continue after systems are retired.
During audits, regulators expect verifiable evidence of access control, retention enforcement, and audit activity, often within days. When historical PHI is dispersed across legacy platforms and unmanaged archives, producing that evidence becomes difficult or impossible.
As systems are retired and teams change, organizations lose the ability to answer basic HIPAA questions:
- Who accessed this PHI?
- Why was it retained?
- What controls were in place at the time?
Because HIPAA obligations extend to historical PHI, organizations remain accountable for demonstrating access control, retention, and auditability after applications are decommissioned.
In audits or investigations, regulators expect verifiable evidence within compressed timelines. Fragmented storage across legacy systems and unmanaged archives frequently prevents organizations from meeting this requirement.
A HIPAA data governance model for historical PHI addresses this gap by defining ownership, enforcing consistent access and retention rules across all data stores, and preserving auditable records even after source systems are retired.
Without a clear governance model, historical PHI becomes a hidden compliance risk over time.
This blog focuses on how to maintain enforceable, audit-ready governance over historical PHI as healthcare systems evolve.
The Building Blocks of HIPAA Data Governance
1. Data Classification
HIPAA governance begins with identifying and classifying data. Organizations must distinguish PHI, ePHI, PII, and non-sensitive data to determine access rights, retention periods, and required safeguards.
2. Data Ownership and Stewardship
Clear accountability is essential. Data owners define appropriate use, data stewards ensure policy adherence and data quality, and IT and security teams enforce technical controls. Defined roles make governance decisions consistent and enforceable.
3. Access Control and Identity Management
HIPAA requires PHI access to be limited to authorized users based on roles and necessity. This includes role-based access control, strong authentication, individual user accountability, and periodic access reviews, all of which must be auditable.
4. Data Security Controls
Technical safeguards protect PHI from unauthorized access or loss. These include encryption, network and endpoint security, and backup and recovery controls. Protections must apply equally to active and archived data.
5. Data Lifecycle Management
HIPAA governance applies across the full data lifecycle. Organizations must define how PHI is created, used, archived, retained, and securely disposed of or anonymized, including adherence to HIPAA’s minimum six-year documentation retention requirement.
6. Audit, Monitoring, and Reporting
Continuous monitoring is required to demonstrate compliance. Organizations must track access to PHI, maintain audit logs, and produce evidence quickly during audits or investigations.
Also read: Healthcare Data Migration: The Ultimate Guide
Common PHI Data That Drives HIPAA Governance Risk
The sections below highlight the common forms and locations where PHI data persists over time and where governance gaps typically emerge.
1. Clinical Records:
Clinical records are the core source of PHI and are typically stored in EHR or EMR systems. They include clinical notes, lab and diagnostic results, imaging and reports, medication records, care plans, and discharge summaries. A significant portion of this data is unstructured, which complicates access control and auditability.
2. Billing, claims, and financial records:
Financial records become PHI data when they are linked to a patient’s identity. This includes insurance claims, billing statements, payment histories, prior authorizations, and EOBs. Although often managed outside clinical systems, these records are subject to the same HIPAA requirements.
3. Administrative and operational records
Operational data qualifies as PHI data when tied to an identifiable patient. Examples include registration and intake of forms, appointment scheduling, referrals, and coordination of care records. These records are often distributed across multiple systems and easily overlooked.
4. Patient identifiers and demographic data
Identifiers such as names, contact details, MRNs, Social Security numbers, health plan IDs, biometrics, and identification photos become PHI when associated with health information.
5. Digital Communications Containing PHI
PHI frequently exists outside core systems in emails, patient portal messages, texts, chats, and call recordings that include patient identifiers. These communications require the same governance controls as clinical records.
6. Derived and secondary PHI
Derived PHI includes reports, data extracts, analytics datasets, archived copies, and exports from legacy systems. These copies remain regulated even when removed from their source applications.
7. Archived and Historical PHI
Inactive data remains in scope under HIPAA. Archived EHR data, retired system databases, long-term storage copies, and audit repositories retain full regulatory obligations regardless of age or usage.
Ready for actionable insight into the DNA of your data?
Governing Historical PHI Under HIPAA: Access, Retention, and Audit Controls
1. Access Control for Historical PHI
| Access Control Aspect | Details |
|---|---|
| Purpose | Ensure only authorized individuals can access PHI retained for regulatory, legal, or compliance purposes. |
| HIPAA Requirement | HIPAA requires secure, system-enforced controls to ensure electronic PHI is accessible only to authorized users. |
| Role-Based Access Control (RBAC) | Access granted based on job role (e.g., auditor, compliance officer, legal team) |
| Least Privilege | Users receive only the minimum access required, especially critical for archived and legacy data |
| Authentication Controls | Multi-factor authentication (MFA) for accessing historical datasets |
| Segregation of Duties | Prevents the same user from accessing and modifying archived PHI |
| Archived System Access | Historical PHI must not remain broadly accessible after system decommissioning |
2. Retention of Historical PHI
| Retention Aspect | Details |
|---|---|
| Purpose | Retain required records for mandated periods while minimizing long-term risk |
| HIPAA Requirement | Policies, procedures, access logs, audit records, authorizations, and consents |
| Retention Period | 6 years from the date of creation or last effective date (state laws may require longer) |
| Retention Schedules | Clearly define retention periods by PHI category |
| Legal Hold Management | Suspend deletion during litigation or investigations |
| Secure Archival Storage | PHI should be immutable (WORM/tamper-resistant), encrypted, and indexed |
| Defensible Disposal | Secure deletion or anonymization once retention obligations expire |
3. Audit Trails for Historical PHI
| Audit Trail Aspect | Details |
|---|---|
| Purpose | Maintain a complete record of PHI access and activity for audits and investigations |
| HIPAA Audit Requirement | Record system activity, monitor access patterns, and detect unauthorized behavior |
| User Identity | Capture who accessed the PHI |
| Timestamp | Record the date and time of access |
| Action Type | Log actions such as view, modify, export, or delete |
| System Accessed | Capture IP address or device details where applicable |
| Immutable Logs | Audit logs must be tamper-proof and securely retained |
| Centralized Monitoring | Aggregate logs from multiple systems into a unified view |
| Retention Alignment | Audit logs are retained at least as long as the associated PHI |
Data Security and Compliance Guide
Learn how Archon Data Suite tackles security and compliance in this whitepaper, ideal for CIOs and IT Managers.
How Archon Data Store Enables HIPAA Data Governance?
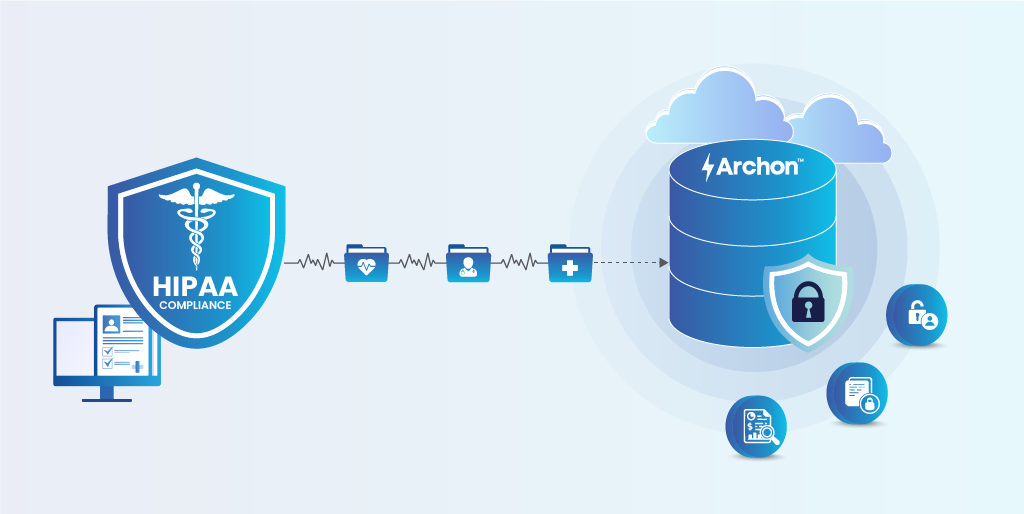
Archon Data Store is a compliance-grade data governance and archival platform designed to help healthcare organizations maintain enforceable HIPAA controls over historical PHI. It applies access control, retention of governance, and auditability directly at the data layer, independent of source applications.
What Archon Does:
✅Centralized Historical PHI Repository: Consolidates PHI from active EHRs, legacy systems, archives, backups, and exports into a single governed data layer.
✅HIPAA-Aligned Access Control: Enforces role- and purpose-based access aligned with HIPAA’s minimum necessary standard, preventing unauthorized or excessive access to historical PHI.
✅Preservation of Data Context and Lineage: Retains original structure, metadata, timestamps, and source relationships so historical PHI remains accurate and legally defensible.
✅Enforceable Retention and Legal Holds: Applies policy-driven retention rules and legal holds at the record level, ensuring PHI is retained with regulatory and legal obligations.
✅Immutable, Searchable Audit Trails: Captures every search, view, and export event in tamper-proof audit logs, enabling defensible evidence during audits.
Patient3Sixty is Archon’s flagship product for the healthcare industry. It provides
- A unified, 360-degree view of a patient’s health record across multiple EHR/EMR historical systems.
- A comprehensive view of patient clinical records.
Learn how Patient3Sixty provides clinical teams with secure access to complete patient histories without compromising HIPAA compliance. Connect with our experts.