Key Points:
- Defensible deletion in enterprise archives is not triggered by retention expiry alone. It requires proof that archived data from retired systems is truly safe to remove.
- After application retirement, teams often lose the business context needed to understand what archived data represents and whether it still has audit, legal, or reporting value.
- Standard deletion tools can execute policy-based deletion, but they often cannot support defensible deletion for legacy ERP, SAP, and long-retained historical records.
- Archon Data Store enables defensible deletion by managing retired application data in a governed archive, preserving business context, and supporting review and exception handling before deletion.
- To be defensible, deletion must leave an audit-ready record of what was deleted, why it was eligible, what reviews occurred, and who approved it.
Defensible deletion sounds straightforward until you apply it to archived enterprise data.
If you are managing data from retired applications, decommissioned ERP systems, legacy platforms, or historical business records preserved after migration, deletion is no longer just a policy action. It becomes a governance decision that must hold up under legal, compliance, and audit scrutiny.
That is what makes enterprise archives different.
In a standard environment, a retention period expires and a disposition event is triggered. In an enterprise archive, that is rarely enough. Once the source application is gone, your teams often lose the business context needed to understand what the archived data represents, why it was retained, and whether deleting it could create risk later.
That is why defensible deletion in enterprise archives cannot rely on a delete rule alone. It has to begin with how archived data is governed after system retirement.
Why Defensible Deletion Matters
Before getting into how defensible deletion works, it helps to be clear about why it is a business priority and not just a governance exercise.
Every byte of data your organization retains carries a cost. Storage is not free, and neither is the operational overhead of managing, protecting, and producing data on demand. Deleting data that has passed its retention period directly reduces your Total Cost of Ownership.
But the more significant risk is legal, not financial.
In litigation, your organization is legally required to produce any data it possesses. If you hold data beyond its retention period and that data contains unfavorable evidence, it can be used against you. Keeping data you are not obligated to keep is not a safe default. It is a liability.
There is also the Right to Erasure to consider. Regulatory frameworks including GDPR require physical deletion of personal data on request. Hiding records from a user interface does not satisfy that obligation. The data must be gone.
The organizations that manage this well have made one important shift: they treat deletion as a default, not a reaction. Rather than deleting data when someone asks, they delete it automatically when it is no longer needed. That shift from reactive to proactive is what a governed defensible deletion framework enables.
The cheapest and most secure byte of data is the one that no longer exists. Defensible deletion ensures your organization only pays for, protects, and manages data that still generates business value.
Why Standard Deletion Approaches Fall Short in Enterprise Archives
Standard deletion approaches can struggle even in structured environments, especially when organizations are dealing with fragmented repositories, inconsistent policy enforcement, legal holds, or unclear ownership of historical data.
Most platforms can apply retention rules, trigger review workflows, and execute deletion actions. Those capabilities matter, but they do not automatically make deletion defensible in enterprise archives.
The challenge becomes much harder when your archived data comes from:
- Retired enterprise applications
- Decommissioned SAP and ERP systems
- Legacy platforms preserved after migration or consolidation
- Historical business datasets retained for audit or compliance
- Structured records stored long after the original system was shut down
In these scenarios, the real issue is not whether a policy can expire. The real issue is whether your organization can still assess the archived data with enough confidence to delete it safely and justify that decision later.
That means answering questions such as:
- Can your teams still understand the historical business meaning of the data?
- Can you assess whether the data still supports audit, legal, or reporting obligations?
- Can you apply deletion consistently across archived records from retired systems?
- Can you clearly explain later why the data was safe to remove?
THE CORE GAP
Policy execution tells you a retention date has passed. Defensible deletion tells you the data was safe to remove, who approved the decision, and why no legal, compliance, or business obligation remained unresolved. Those are very different standards.
If archived data has become fragmented, disconnected from its original business context, or difficult to interpret after system retirement, a policy-driven deletion process alone is not enough. You need an enterprise archiving approach that keeps historical data governed, understandable, and auditable throughout its lifecycle.
That is exactly where Archon’s defensible deletion capability is designed to stand out.
How Archon Enables Defensible Deletion in Enterprise Data Archives
Archon is not a platform that simply deletes data after a retention date expires. It is an enterprise archiving platform built to manage historical business data after the source application is retired.
Instead of treating deletion as a standalone event, Archon enables your organization to apply defensible deletion as part of a governed archive lifecycle. Here is what that looks like in practice.
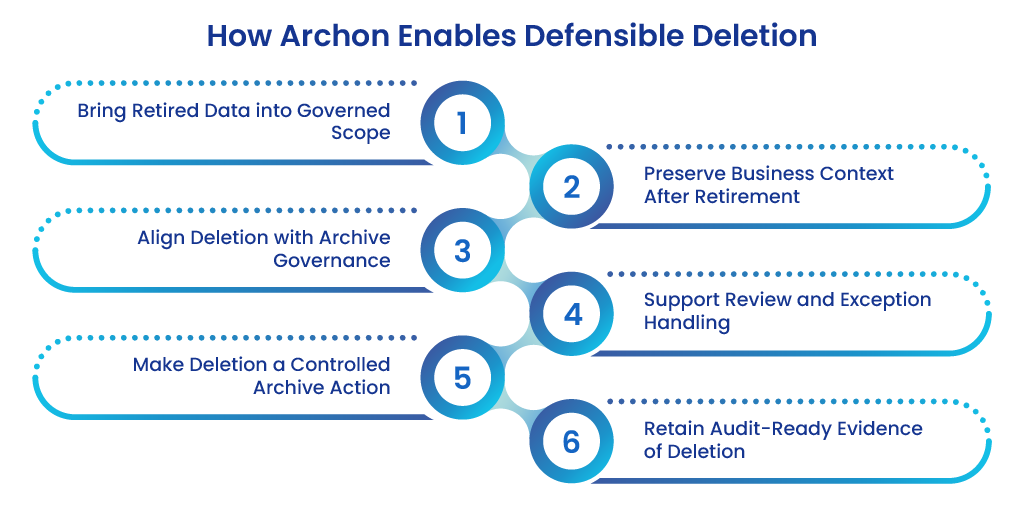
1. Brings Retired Application Data into a Governed Archive Scope
Defensible deletion starts with control.
If your historical data remains spread across disconnected archive repositories, extracted legacy datasets, or retired system outputs, deletion becomes risky because your teams lack the complete context needed to make confident deletion decisions.
Archon addresses that by bringing retired application data into a governed enterprise archive framework. At the point of ingestion, every structured record or dataset is assigned a Data Passport, a functional metadata mapping that links the record to a specific retention policy and a named data owner.
This is not just a timestamp. It is the Policy DNA of the record, establishing a defined expiry, a clear ownership chain, and a predictable lifecycle roadmap from the moment the data enters the archive.
That gives your teams a stronger foundation for defensible deletion because archived data is no longer treated as scattered legacy residue. It becomes part of a controlled archive scope where retention, access, lifecycle, and deletion decisions can be managed consistently.
Without that governed archive scope, defensible deletion remains difficult to operationalize at scale.
2. Preserves Business Context After the Source Application Is Gone
One of the biggest challenges in archived enterprise data is that the source application disappears, but the accountability does not.
Once a system is retired, archived data often loses the business context that made it understandable in the first place. Your teams may still have the records, but they no longer have the application logic, process visibility, or practical context needed to evaluate what the data means.
That makes deletion harder and riskier.
Archon is designed to preserve access to historical business data outside the original application, so your teams can still evaluate archived records with the context needed to make sound lifecycle decisions.
That helps your organization assess:
- What the historical record represents
- Which business process it supported
- Why it was retained after system retirement
- Whether it still carries compliance, reporting, or audit value
- Whether deleting it could create gaps in historical accountability
Defensible deletion becomes significantly stronger when decisions are based on preserved archive context, not just expiry dates and retention metadata. That is a distinction many platforms struggle to maintain after application retirement.
3. Aligns Deletion with Archive Governance, Not Just Policy Expiry
In many environments, deletion is treated as a simple end-of-life event. A retention rule expires, and the platform is expected to remove the data. That approach is often too narrow for enterprise archives.
With Archon, deletion is approached as part of archive governance. The platform continuously scans the archive’s metadata registry against each record’s assigned retention policy.
When records reach their end-of-life, they are surfaced as a Candidate List, a transparent, auditable preview of records eligible for removal. This automated scanning shifts the burden from manual IT oversight to a system-driven governance model, ensuring your archive does not become an unmanaged accumulation of expired data over time.
Critically, generating a Candidate List is not the same as triggering deletion. Before any deletion proceeds, every candidate record is cross-referenced against a hold registry.
If any record, or the entity it belongs to such as a specific vendor, contract, or project, is flagged for an ongoing audit, investigation, or legal matter, it is immediately locked and removed from the deletion queue.
This legal hold check is the most important safety gate in the process. It ensures your organization remains compliant with duty-to-preserve obligations and prevents the accidental destruction of data that could carry severe legal consequences.
Your teams can therefore assess:
- Whether the archived data still has a valid retention obligation
- Whether legal or compliance exceptions still apply
- Whether historical access needs still exist
- Whether the archived records are part of a broader scope that requires review before deletion proceeds
- Whether deleting the data would affect the auditability of retained historical records
This is the difference between generic disposition logic and a more defensible enterprise archive model.
4. Supports Review and Exception Handling Before Deletion
Not every archived dataset should be deleted automatically.
Some records may require legal review. Others may need business sign-off, exception handling, or validation that no unresolved obligation still exists.
This is especially true for data retained after application retirement, where the source system no longer exists to provide easy verification.
Archon supports a governed steward approval process in which data owners and compliance officers are presented with a summary of pending deletions through a governance dashboard.
They can review candidate records, verify the logic applied, and provide a digital authorization before any purge proceeds. That digital sign-off transforms a technical action into a documented business decision, creating an accountable trail that proves deletions were reviewed by qualified personnel rather than triggered by an automated process alone.
To keep this process from stalling, approval SLAs should be defined clearly. Data stewards should be given a set window, for example, 14 days, to review and authorize.
If no action is taken within that window, the process should escalate to a designated data privacy officer, pause for manual review, or follow a pre-agreed escalation path based on the organization’s governance policy.
This is how Archon turns defensible deletion from policy theory into an operational archive process.
5. Makes Deletion a Controlled Archive Action
Once archived data is confirmed as eligible and authorized, deletion still has to be executed in a way your organization can defend later.
Archon’s advantage is that deletion happens within a governed archive framework in two distinct stages rather than as a single disconnected cleanup task.
The first stage is a soft delete. Once approved, records are logically erased and removed from all user-facing search indexes and application views. The data becomes invisible to the business, but the physical bits remain in the storage layer for a defined cooling-off period, typically 30 days.
This serves as an insurance policy against human error. If a steward or reviewer realizes a mistake was made, the record can be recovered before permanent destruction occurs.
At the conclusion of the cooling-off period, a hard purge is initiated. This is the point of no return. Data is physically and permanently destroyed from the storage layer.
For structured data, this involves reclaiming the underlying storage space. For unstructured records, it involves a permanent purge from the object store. This is where the tangible benefits of defensible deletion are realized: reduced storage costs, smaller attack surface, and a demonstrably cleaner archive estate.
Your organization can maintain clarity around:
- What archived data was in scope
- Why it became eligible for deletion
- What reviews or exceptions were considered
- What decision was made, and who authorized it
- What action was ultimately executed and when
This makes deletion easier to explain because it is part of a controlled archive process, not just a background action.
6. Helps Retain Audit-Ready Evidence of Deletion Decisions
If you cannot explain the deletion later, it is not defensible.
That is especially true in enterprise archives, where historical data may have been retained for years and may still be subject to legal, regulatory, or audit questions long after the source application is gone.
Because Archon treats deletion as part of archive lifecycle governance, every completed deletion generates a Certificate of Destruction. This is an immutable Tombstone Record that captures the who, what, when, and why of the deletion.
It contains the unique cryptographic hash of the deleted record, the retention policy that authorized its destruction, the digital signature of the approving steward, the method of destruction, and the precise timestamp of the hard purge.
Critically, no personally identifiable information or sensitive business data is retained in the certificate itself.
If a regulator or auditor asks for a record years after deletion, your organization can produce this certificate as evidence that the data was not lost or mishandled, but was disposed of through a professional, governed, and legally compliant process.
Your organization is therefore in a much stronger position to demonstrate:
- Why was the data retained
- Why it became eligible for deletion
- What reviews or exceptions applied
- Who authorized the decision
- What action was executed and when within the archive scope
This is what turns deletion into something you can defend, not just something you can say happened.
Why Archon Is the Right Foundation for Defensible Deletion in Enterprise Archives
Defensible deletion in enterprise archives is not a capability you switch on at the end of a retention schedule. It is the outcome of having archived data governed, interpretable, and auditable from the point of application retirement onward.
That is why Archon’s defensible deletion capability is especially relevant for SAP and ERP retirement initiatives, legacy application decommissioning, historical data retained after cloud migration, legacy archive consolidation efforts, and compliance-driven deletion of long-held structured records. In these environments, the challenge is not simply whether data can be deleted. The challenge is whether it can be deleted in a way that remains controlled, explainable, and defensible after the original application is gone.
To continuously demonstrate the value of this process, organizations should track the metrics that reflect its impact: total storage volume reclaimed, number of Certificates of Destruction issued, and eDiscovery cost avoidance achieved through proactive deletion. These are the figures that make the business case visible to leadership and validate ongoing investment in archive lifecycle governance.
As an enterprise archiving platform, Archon enables your organization to operationalize defensible deletion where it is hardest and most important, not just by deleting data when a timer runs out, but by helping you govern archived enterprise data in a way that makes deletion practical, controlled, and defensible.
Ready to put defensible deletion into practice in your enterprise archives? See how Archon can help.